Signing an App using a CodeSign certificate with SignTool & Windows 10
I was recently working with a new Windows app we built at CleanBrowsing and our users were getting hit with security warnings post-installation. This warning was generated because the app was not signed.
Ok, let’s get things signed.
To sign I would need a code-sign certificate. I went through the process of getting an Extended Validation (EV) certificate from GlobalSign.
Site Note: The process was not too bad, you sign some forms, take some pictures and you’re done. You do need a Windows machine when download the certificate, be prepared for that.
This biggest annoyance is that you need Internet Explorer to download the certificate and install it on your token. I had to download IE 11 to get this done. Yes, I tried with MS Edge, and other modern browsers but nothing worked.
Couple of Prerequisites to be aware of:
- SafeNet (You will get your token from this organization)
- Windows SDK (Using Windows 10)
Be aware that signing will be done via the Windows command prompt. Pay special attention to where the SDK is installed.
PROCEED AFTER YOU HAVE RECIEVED TOKEN AND INSTALLED CERT
Step 1: Open Command Prompt in Administrator Mode
Step 2: Set Working Directory to SignTool Directory
Using Windows 10 SDK, in 2021, this was my working directory for SignTool
cd “\Program Files (x86)\Windows Kits\10\bin\10.0.19041.0\x64
Step 3: Set appropriate options
This is what my command looked like when I was done:
signtool sign /a /tr http://rfc3161timestamp.globalsign.com/advanced /td SHA256 “C:\Users\[User name]\path\to\file.exe”
Options Used:
/a = automatically set the name according to what was on the certificate, if you want to set it differently I believe you use /n “subject name”
/tr = This sets the timestamp, and the “r” option references a RFC3161 compliant trusted time stamp. Each CA will have a timestamp you can use. For example Globalsign uses: http://rfc3161timestamp.globalsign.com while DigiCert uses: http://timestamp.digicert.com
(note: the irony of those not using HTTPS is not lost on me)
/td = This sets the timestamp algorithm to use, the recommended configuration is SHA256 so just use that and save yourself the headache. Every provider will do this a bit differently. For GlobalSign, it only works if you use /advanced in the slug the way I have it: http://rfc3161timestamp.globalsign.com/advanced with the /td SHA256
” “ = Lastly, make sure you put the path to the executable you are trying to sign, include the double quotes.
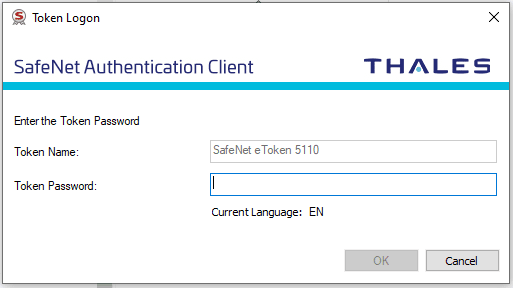
When you hit enter, it will ask you for the token password ( I hope you haven’t forgotten it):
When it’s done, you’ll get this output in your command prompt:
Done Adding Additional Store
Successfully signed: C:\Users\[User name]\path\to\file.exe
