Secure Your Traffic on Public WiFi
Often when I give talks on website security one of the various discussion points is, and rightfully so, around your individual posture when interacting on the web. This often means being aware of things like transferring your data insecurely over the web.
This insecure act is often achieved through the use public WifI access points (i.e., Starbucks, Airports, Hotels, etc.). The most obvious solution, or what feels like the most obvious is to work off a Virtual Private Network (VPN). When talking to a Network / Systems / Security individual this is the obvious choice, but to the everyday consumer it’s not.
Disclaimer: I am not affiliated with GetCloak in any way, in fact I don’t know the team at all. I just find the product highly effective and useful.
Minor Tangent: Differentiating Between VPN and SSL
It’s important to understand that when I speak transferring data insecurely I’m not referring to transactional type data, although that is one form ofcourse. And when I say transactional data I’m referring to purchases online, or filling out forms with your Personal Identifiable Information (PII).
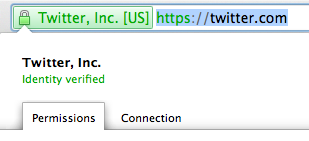
These types of transactions are often achieved through an SSL tunnel and to you, that means you’re looking for things like https:// in the URL address bar in your browser. It’s the green check that helps verify that the individual that you are entrusting with your data is legitimate and it’s safe to continue.
If you’re a website administrator and you’re leveraging OpenSSL on your web server for your transactional activity then please be sure to check and if necessary patch your servers. Heartbleed is a very serious vulnerability that if left unpatched can cause you and your clients undo rest and heart ache.
GetCLoak: A VPN for the Everyday Consumer
Last weekend while giving a talk on Website Security in Minneapolis I was made aware of a really cool service out there known as GetCloak.
As the name implies it cloaks your communication (i.e., creates a personal VPN). I know, how nifty of a name.

This was new for me, as I had never heard of them, but then again I wasn’t really in the market for such a service, at least I didn’t think I was. Prior to them I did what most techs likely do. Purchased a remote, isolated server, running only SSH that I would use any time I traveled and even at home.
While this was convenient enough, it is not and will never be an ideal solution for the masses. Where this becomes a challenge is trying to get my wife or other family members to adopt it. And that’s where you, the everyday users come into play.
The other challenge this presented was I was leveraging SOCKS 5 and binding traffic to a local port on my box. This is great for most of what I do, but where it falls short is for all other traffic outside of my browser. To truly get it implemented right I’d have to configure all my applications to leverage the new ports and not all applications make this process that easy. The other shortcoming to my existing process was with my mobile devices.
Again, a significant hit to the everyday user, not something the less technically inclined would ever adopt.
It’s because of this that during the past few talks I rarely bring up the importance of overall online posture. Applications like GetCloak flip this on its head and bring complex technologies like VPN to the everyday and in my opinion that is revolutionary and powerful.
While I won’t use the Cloak app for business related activities, I will use it when traveling and on the move, for business sensitive communication I’ll continue to lean on my existing processes. It’s not to say that I don’t trust them, it’s just that I trust mine more…
Configuration of GetCloak
The biggest shortfall with the application, it seems, is it’s restricted to iOS applications. Fortunately for me that’s great, not so fortunate for all others but it’s step in the right direction.
Installation is very simple, and best of all you can leverage a free trial for 30 days before making a decision. Double-click the DMG download and follow the default steps. You’ll see the app icon get added immediately and like that it starts working.
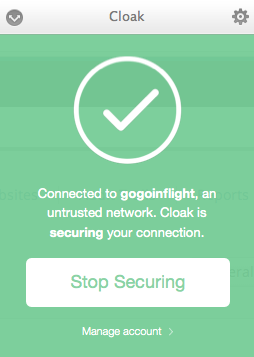
Once installed it’ll configure the VPN and begin securing connectivity. Any time you connect to a public WiFi access point it will detect it and begin securing the connection automatically.
Be sure to install this on you mobile devices as well — iPhone and iPad alike. What I was alluding to before was it’s ability to encrypt all traffic from the devices, not just browser traffic, this means emails, apps, and browser traffic. This is more powerful than many realize and something few actually take into consideration.
Still not convinced?
Not a problem, take some time to go through their documentation and I am sure you’ll come to a similar conclusion as myself and if you travel as much as I do you too will find it’s immediate value. This will definitely be installed on my various boxes, to include the family devices.
If you reveal your secrets to the wind, you should not blame the wind for revealing them to the trees.
Kahlil Gibran
