Over the past couple of years we've been reminded time and time again of how susceptible our communication mediums are to prying eyes. Classic examples of its susceptibility can be seen in the
very public disclosure of General Petraeus affair in 2012, the release of
over 170,000 emails after the Sony compromise in 2014, to the recent
Ashley Madison compromise in which the CEO's emails were shared publicly in 2015.
In either case, the information gleaned from these emails were damaging at best, and destructive at worst. In either case, what we should take away from it is that how and what we say, even if in what we perceive to be secure, is not necessarily the case.
Emails are a treasure trove of information, and as such we should all be spending a bit more time thinking of not only what we say, but how we keep what we say safe from prying eyes.
OpenPGP for Email Encryption
I, like most, spent very little time thinking about my emails and the need for their encryption. It was one of those things I took / take for granted. I'm use Gmail email service for both business and professional needs, I have multiple layers of security control in place, I feel fairly comfortable. Each control however has one fundamental flaw, they're all designed to keep people out, assuming once someone is in, you're good. What if someone does bypass each control? What if they do get in? There in lies the problem, and where encryption can play a critical role.
Like most things with security, getting into a good habit of using encryption can leave a lot to be desired as it's often at the expense of convenience.
OpenPGP is a derivative of the Pretty Good Privacy (PGP) protocol as developed by Phil Zimmerman in 1991; it's a non-proprietary protocol for encrypting email using public key cryptography. In 1997, the Internet Engineering Task Force (
IETF) formed the OpenPGP working group whose focus was to take the once proprietary PGP protocol developed by Zimmermann. It became an IETF
proposed standard under RFC 4880 in 1997, in doing so it's become the preferred means of encrypting emails.
Mailvelope for Webmail Email Encryption
The only way email encryption would work for me, as I assume the same for you, is if it seamlessly integrated into my everyday workflow. That meant it'd need to integrate with my browser, and my browser of choice is Chrome.
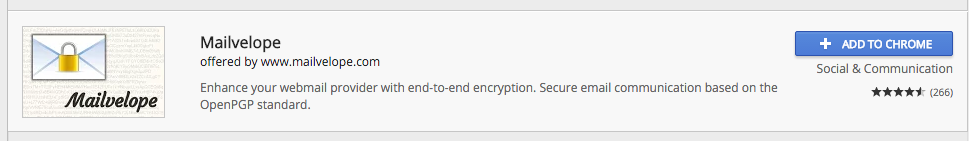
I came across
Mailvelope, and quickly recognized and gained appreciation for its easy integration and ease of use. Mailvelope is a browser based extension that works with the more popular browsers, including Chrome
(I'm not affiliated).
For those concerned, the keys are maintained client side, nothing is shared back with their networks. Yes, there are inherent risks with browser based extensions that maintain things like your Private keys for things like GPG (noted). Like most thing though with security, it comes down to your own individual risk posture.
Configuring Mailvelope with Gmail
If you're interested in giving this a try, here is a quick tutorial to help get you started:
1. Install the extension
If on a Mac, you can navigate to
Windows > Extensions > Get More Extensions and use the search function to look up
Mailvelope.
2. Navigate to the Mailvelope Options Panel
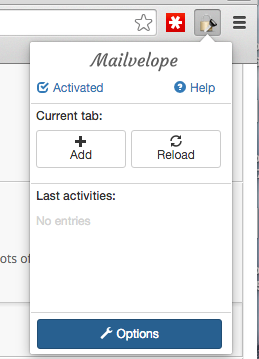
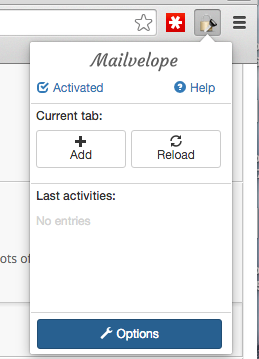
Once the extension is added, it will automatically add a menu option to your browser similar to this:
You'll navigate to the
Options by clicking on the lock with key, and you'll see the options button on the menu:
3. Create Your Private / Public Key Pair
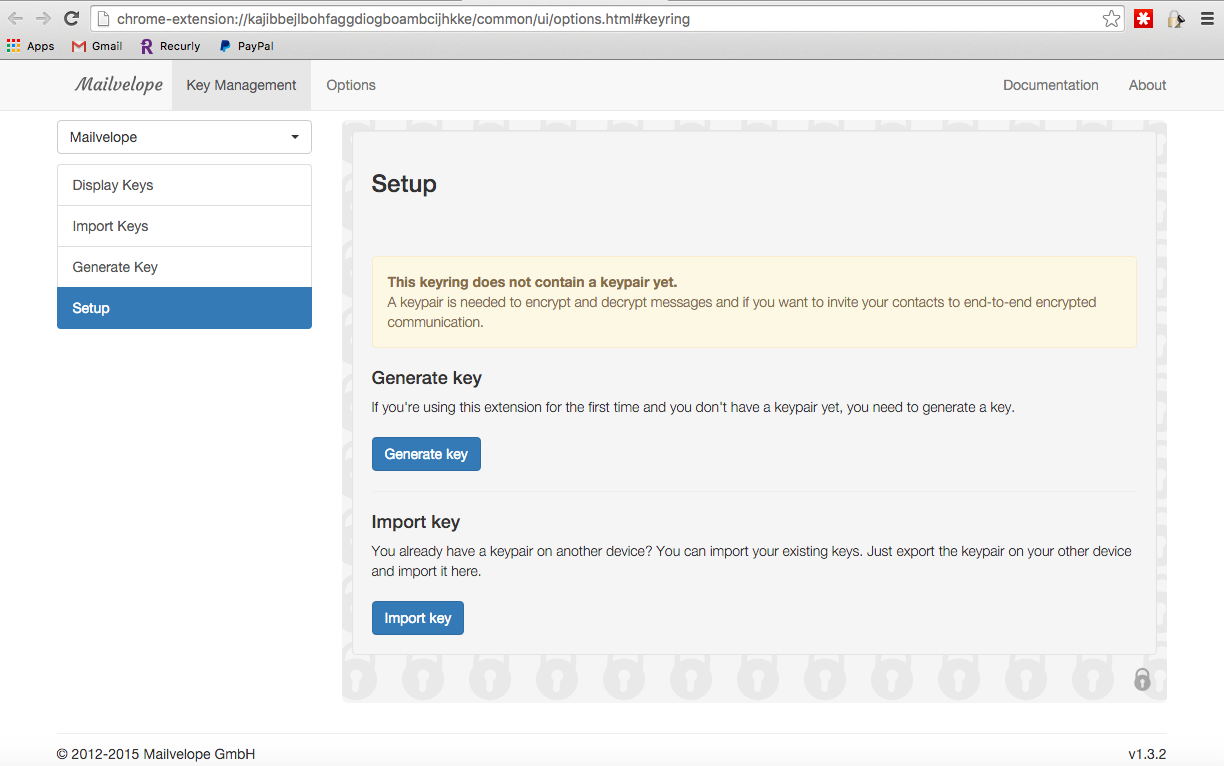
Once on the options page, if you have existing keys you'll be able to upload it. If not, it's just as easy to create a new pair:
The
Generate Key option is what will get you started, and you'll get a page like this:
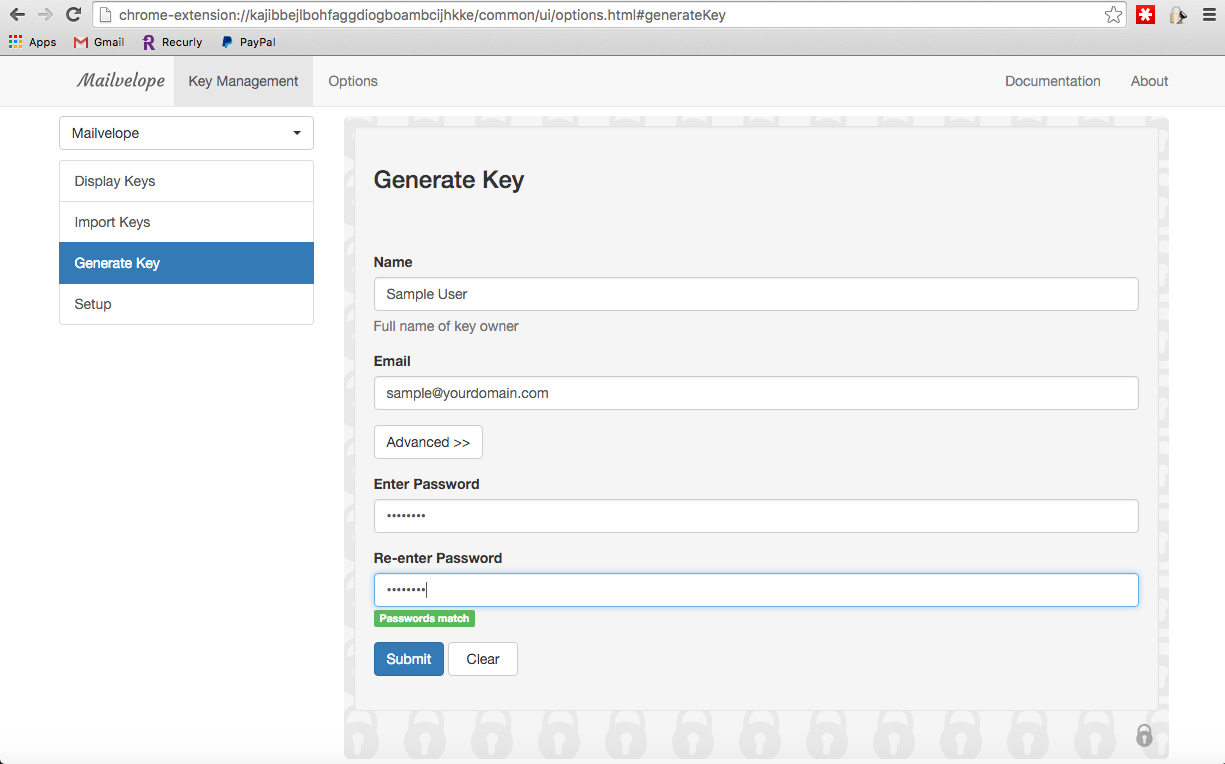
The email is the email you want to have the key for, so if you have multiple emails you could create it for all your emails. The password is what you'll require to decrypt the encrypted emails, so please remember it. Please though, be sure to follow basic rules around password creation -
Complex, Long and Unique.
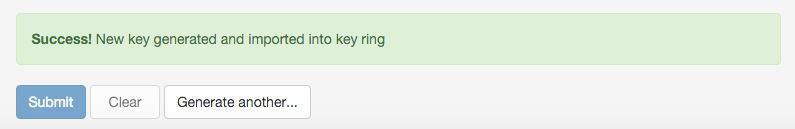
Click Submit, and the key will be generated. You should see a success message if it's successful:
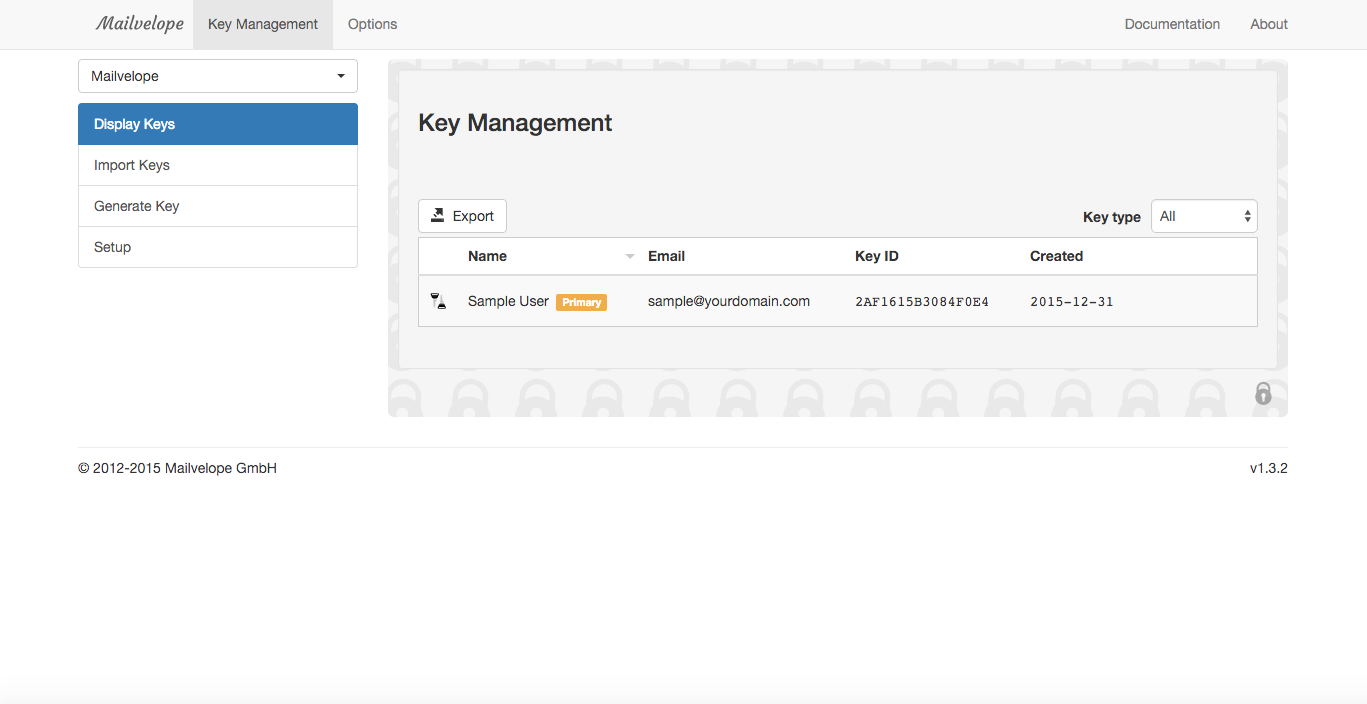
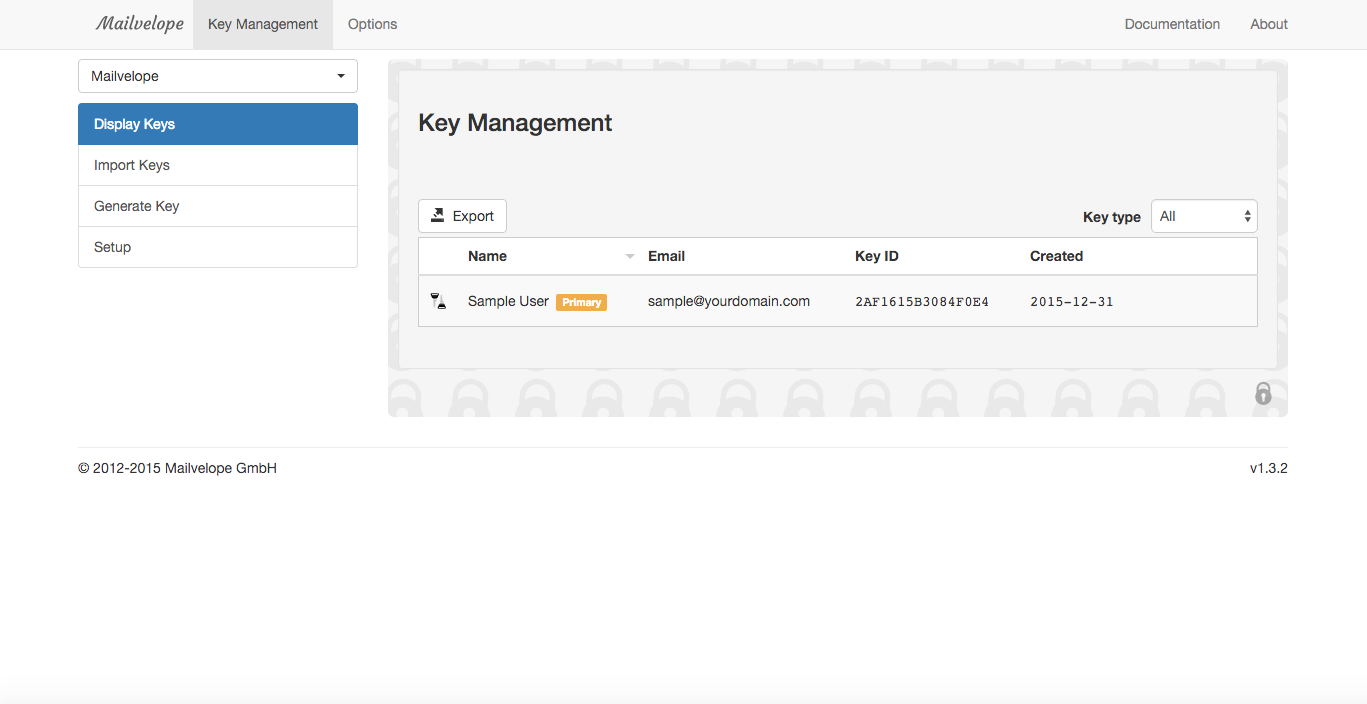
Once done, you'll find the keys in your Key Manager, you'll see it as
Display Keys in the Mailvelop menu options:
4. Add and Share your Public Key
The biggest issue with this will never be the configuration, it'll be that in order for it to work you require people to participate. If not, you have PGP configured and read, but no one to use it with. To share your public key, you can do it this by going to the key details:
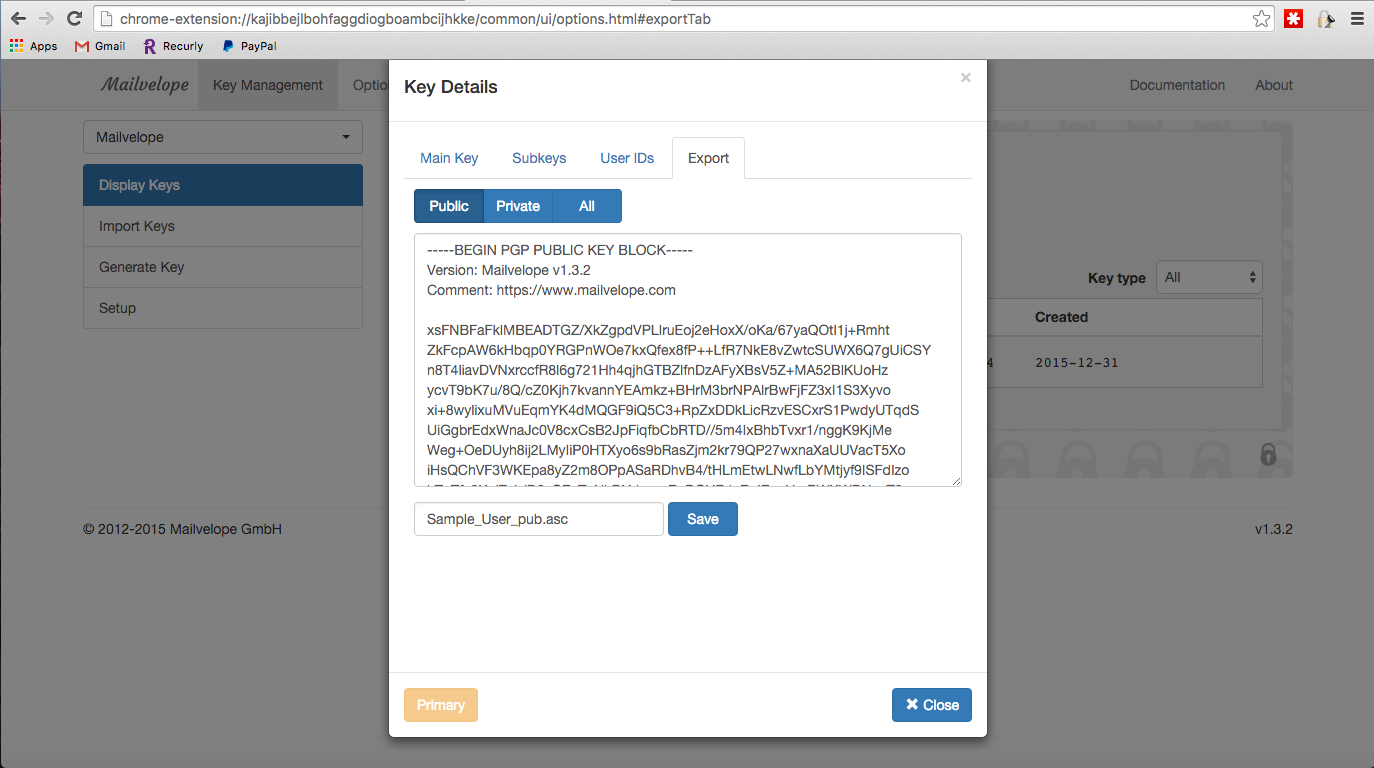
You'll want to share only the
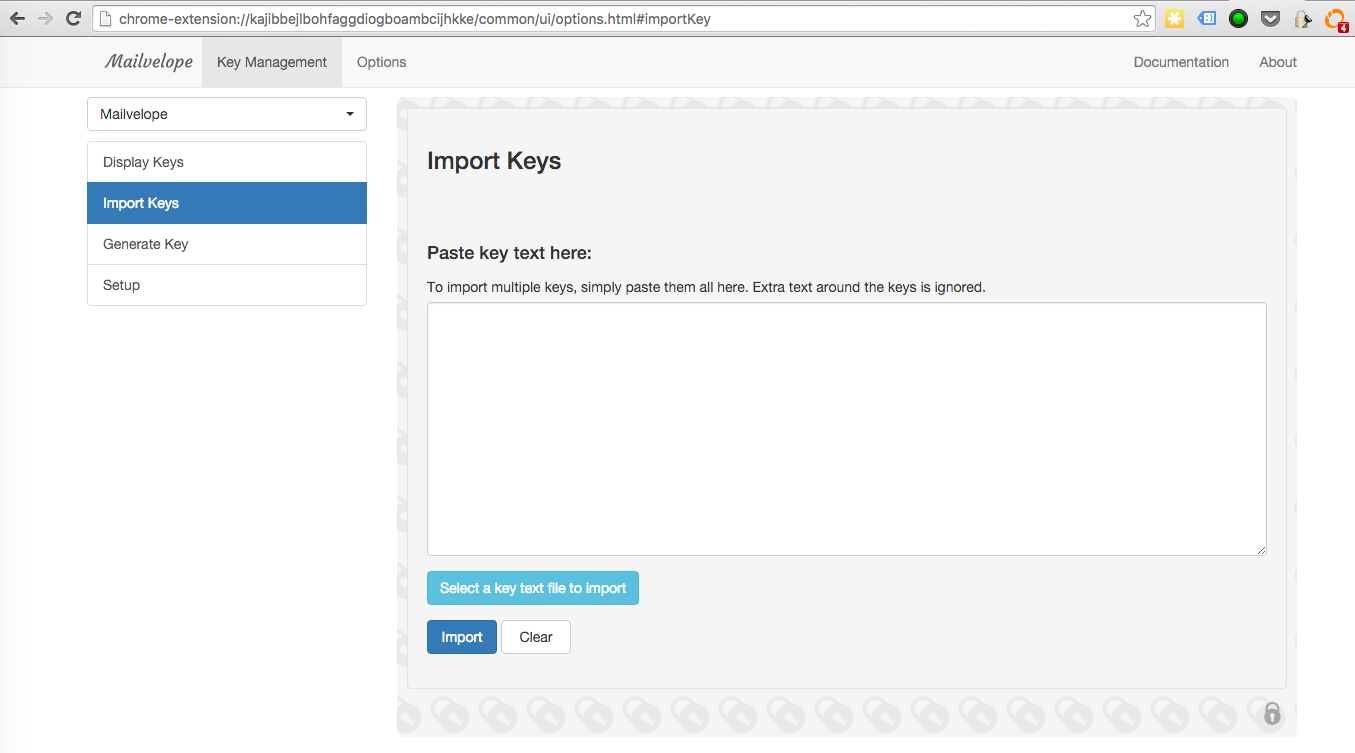
PUBLIC key. The private key is what you keep, you never share this. To import, you'll navigate to Import Keys in the menu options and you'll upload the recipients public key. If you want to test it, you can use
my public key.
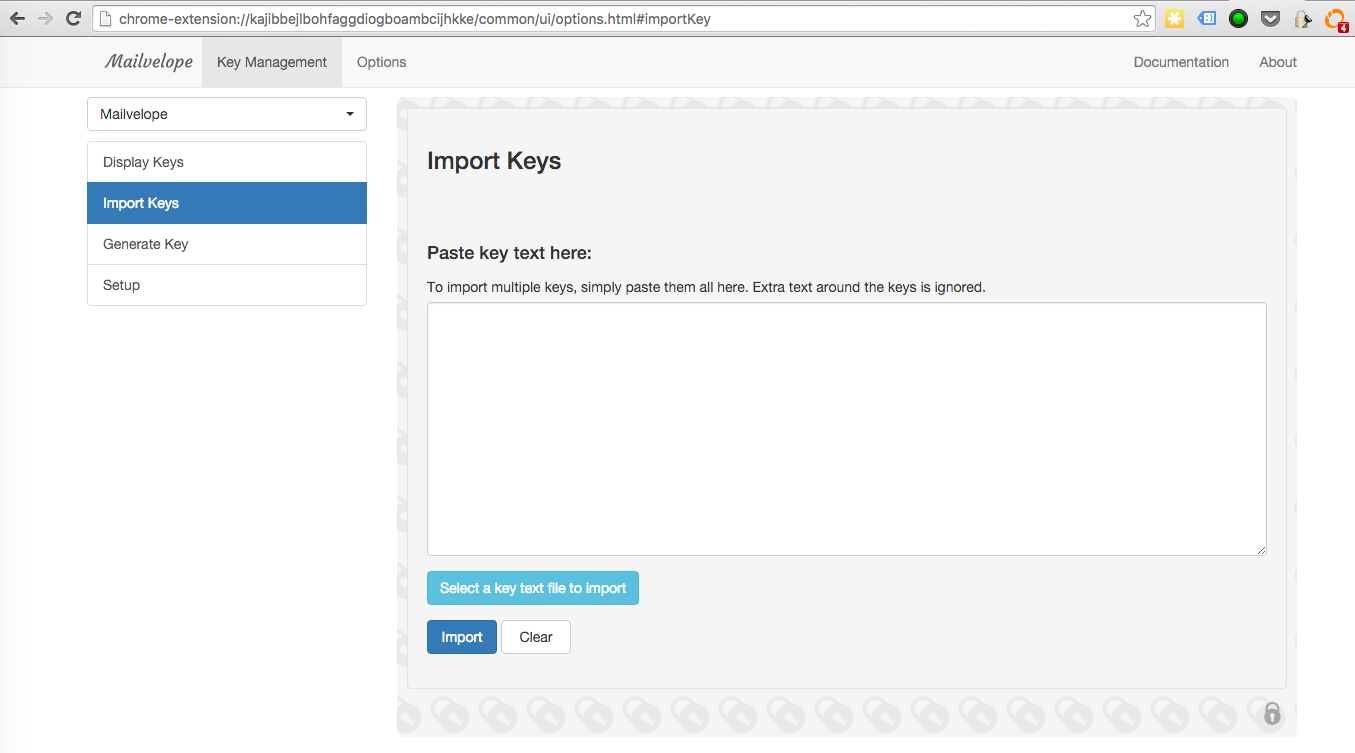
5. Send Your First Encrypted Message
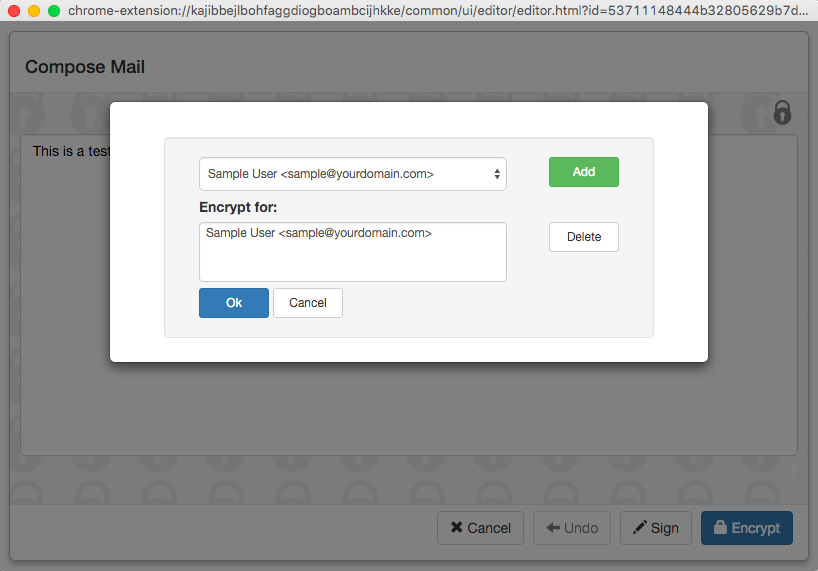
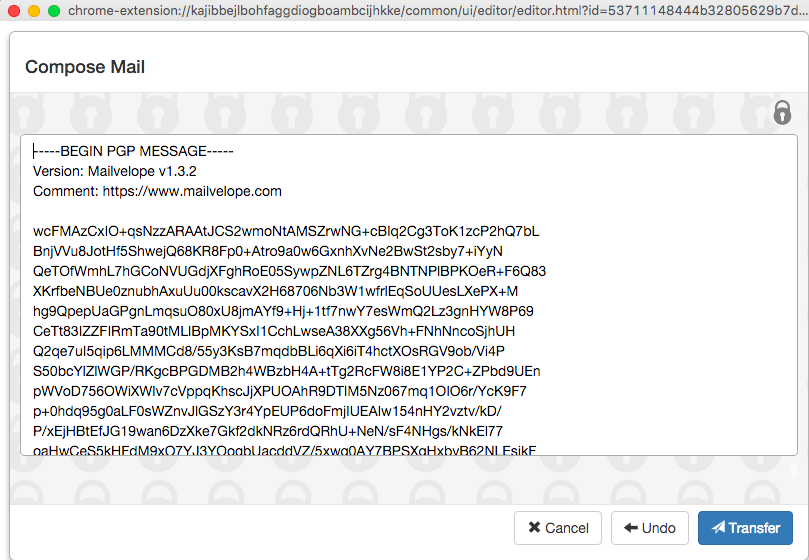
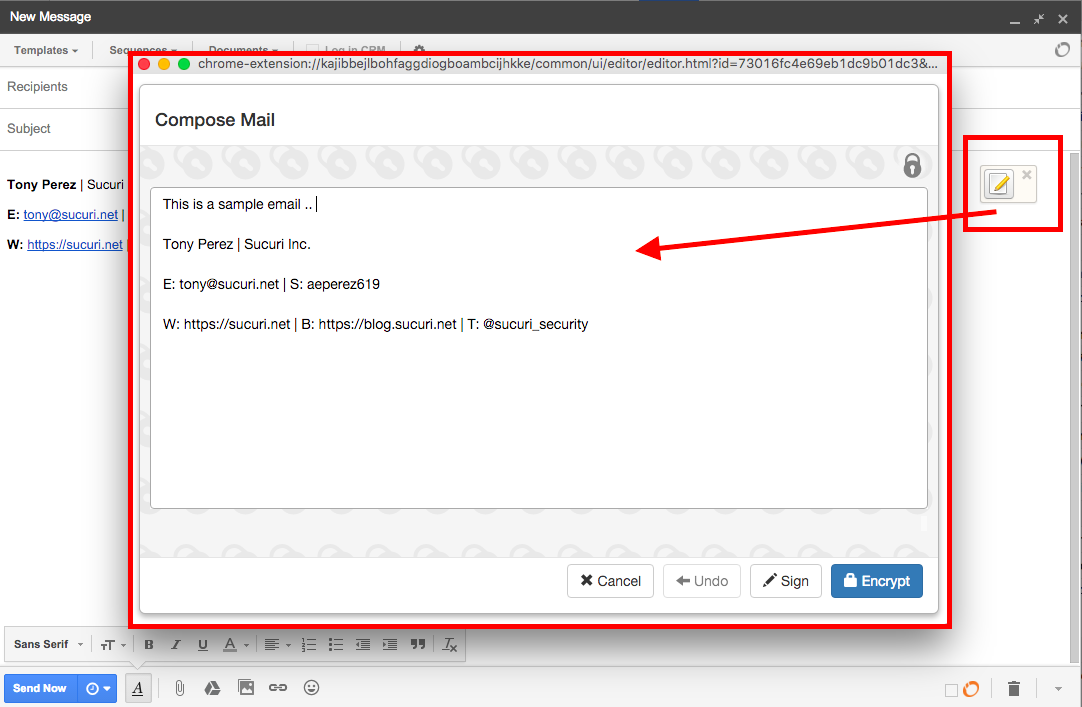
Once you have someone to communicate with, you'll be able to send your first email. You'll open your email client, and you'll find a new option in the email allowing you to encrypt. Click the new editor button in the email, and via the new pop up form start typing your message.
As you can see in the image below, it'll carry over your existing email signature as well.
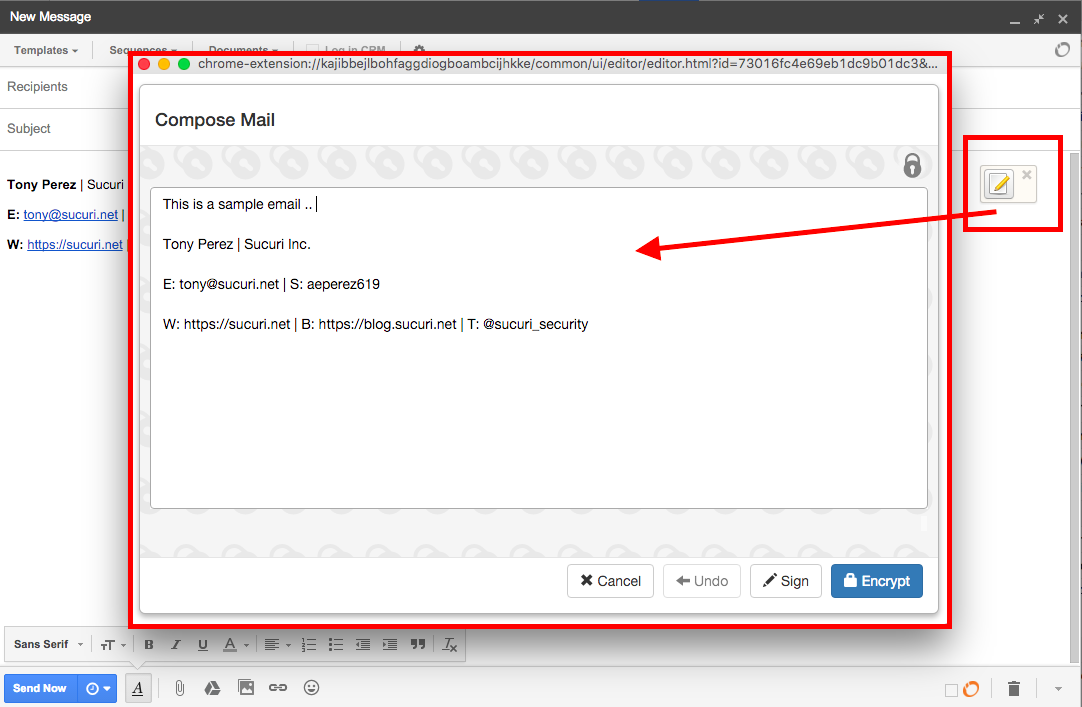
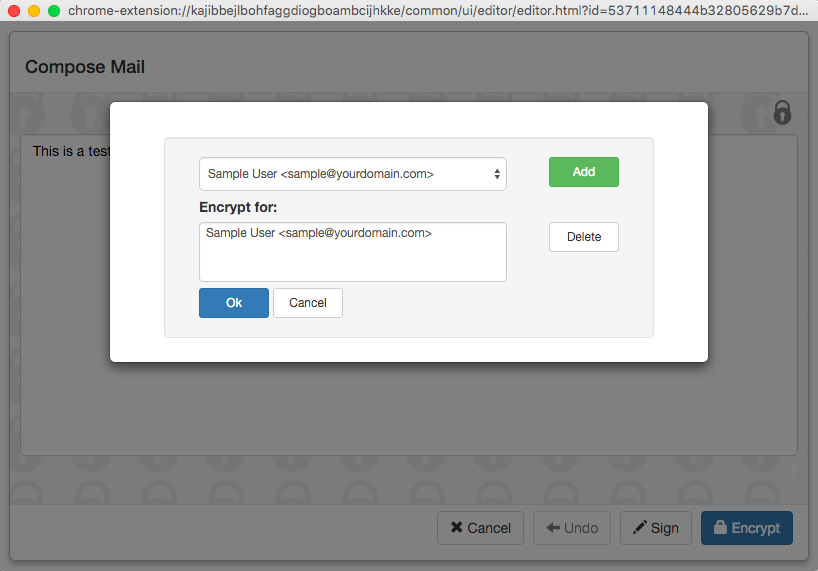
When you're done, click on
Encrypt, and select the individuals you want to encrypt for
(hint: you'll need someone else's public key in order for this work.. ) It's important you select your email, and your recipients email; if you don't, you won't be able to read your own email.
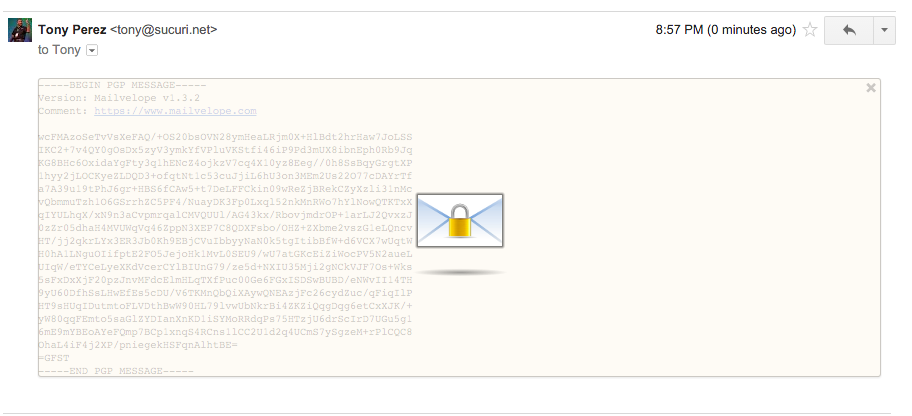
When you click Ok, you'll see what appears to be a garbled mess:
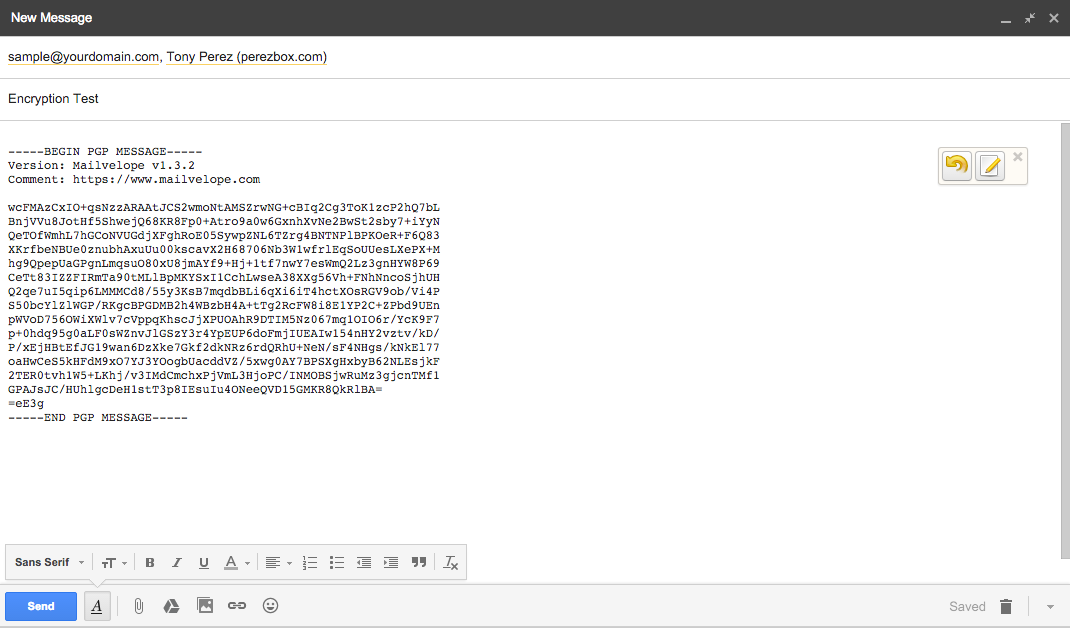
Click on
Transfer and the garbled mess will be pushed to the email, ready for you to send to the recipient.
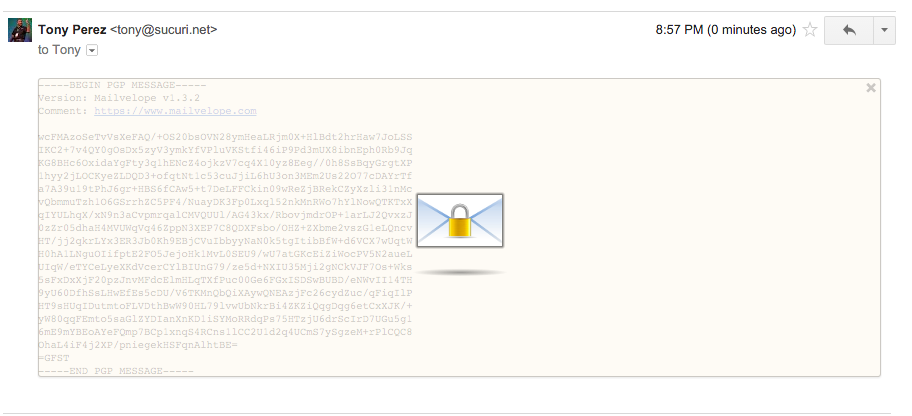
When the recipient receives the message, they'll be able to decrypt the message as long as it was encrypted for the user.
This is what it'll look like when you receive something via the Gmail web client:
The Importance of Privacy
We each depend heavily on the idea that what we say, with those we trust, is being said in confidence. We assume that the various communication mediums we use provide us the security we require, yet the reality is they rarely do. Regardless of the mechanism employed, you have to assume everything you are sharing can and will likely be consumed by someone other than the person you intended at some point. Fortunately, technologies like OpenPGP offer us the means to make this possible and tools like Mailvelope, make it practical.
As a business owner, I can't stress the importance of taking privacy more seriously. Of the various compromises we've seen over the years, the biggest impacts have often come in the form of emails that were released; emails in which information / dialog were had that could be embarrassing or less than favorable when put out of context or the personal relationships are missing that allow for certain things to be said in confidence. When out of context, everything can be impactful and those intent in causing you harm will be quick to use it, and worse yet, the public will be quick to draw conclusions from their perfect perches.
Besides the CYA like explanation above, it's important to employ encryption in critical functions within your organization. Functional groups might include your Finance, Human Resources, or even your Infrastructure teams. Encryption, the importance of Privacy, extends far beyond emails as well, but for now it's a good place to start for most businesses.
Do you account for encryption in your emails?,
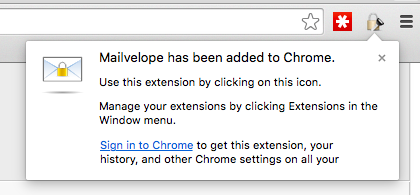 You'll navigate to the Options by clicking on the lock with key, and you'll see the options button on the menu:
You'll navigate to the Options by clicking on the lock with key, and you'll see the options button on the menu:
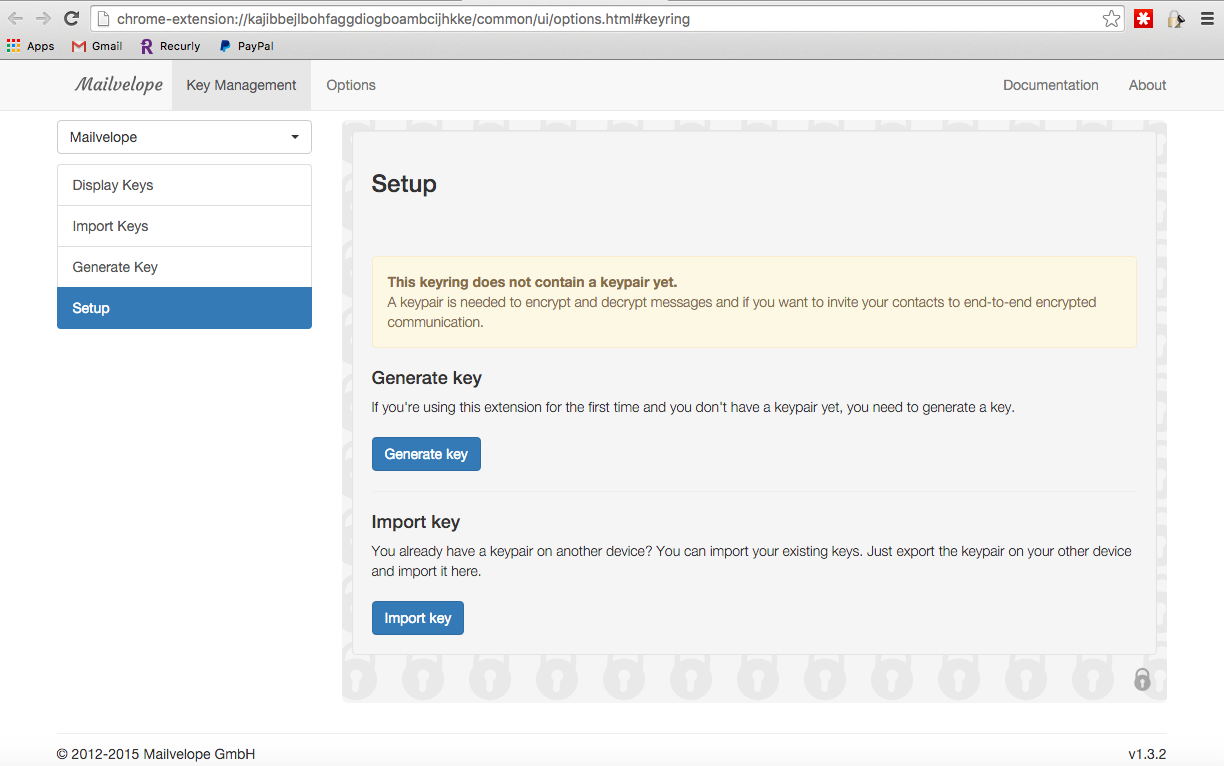 The Generate Key option is what will get you started, and you'll get a page like this:
The Generate Key option is what will get you started, and you'll get a page like this:
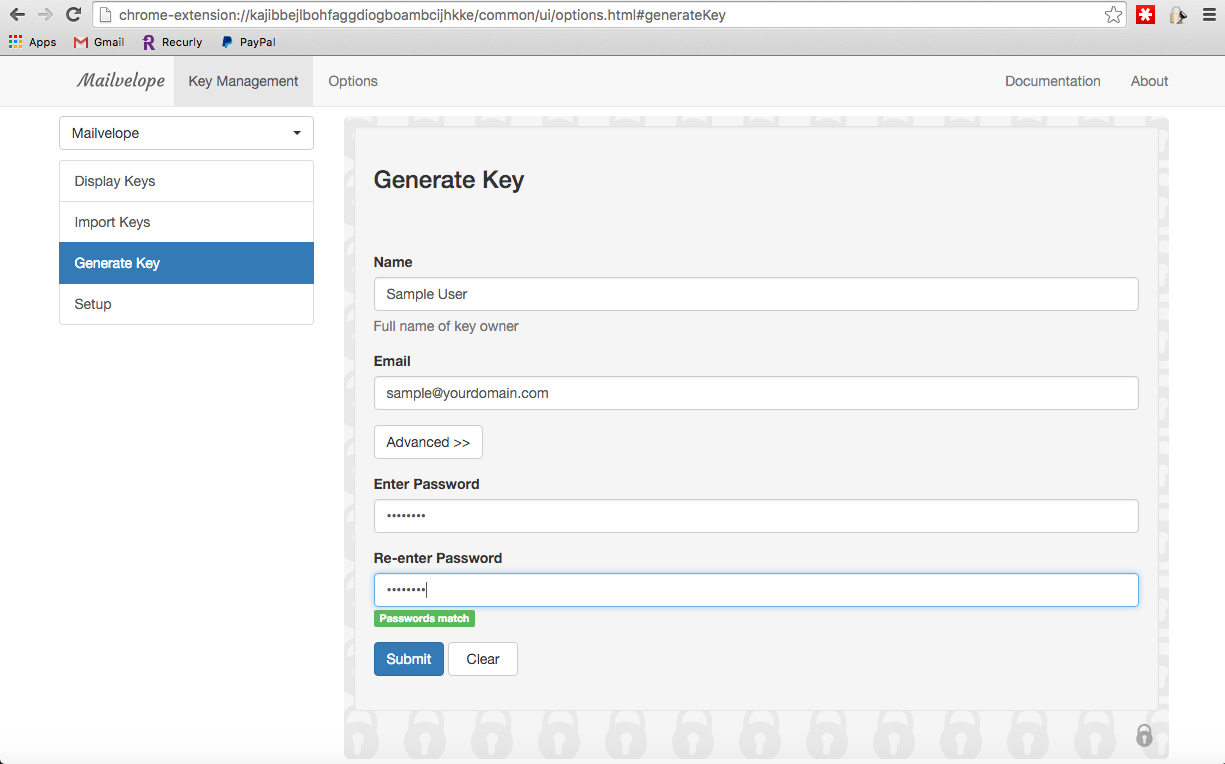 The email is the email you want to have the key for, so if you have multiple emails you could create it for all your emails. The password is what you'll require to decrypt the encrypted emails, so please remember it. Please though, be sure to follow basic rules around password creation - Complex, Long and Unique.
Click Submit, and the key will be generated. You should see a success message if it's successful:
The email is the email you want to have the key for, so if you have multiple emails you could create it for all your emails. The password is what you'll require to decrypt the encrypted emails, so please remember it. Please though, be sure to follow basic rules around password creation - Complex, Long and Unique.
Click Submit, and the key will be generated. You should see a success message if it's successful:
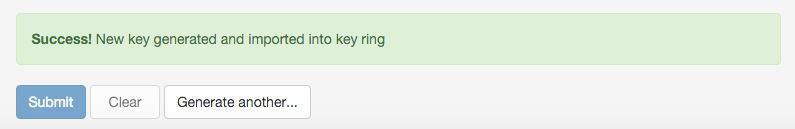 Once done, you'll find the keys in your Key Manager, you'll see it as Display Keys in the Mailvelop menu options:
Once done, you'll find the keys in your Key Manager, you'll see it as Display Keys in the Mailvelop menu options:
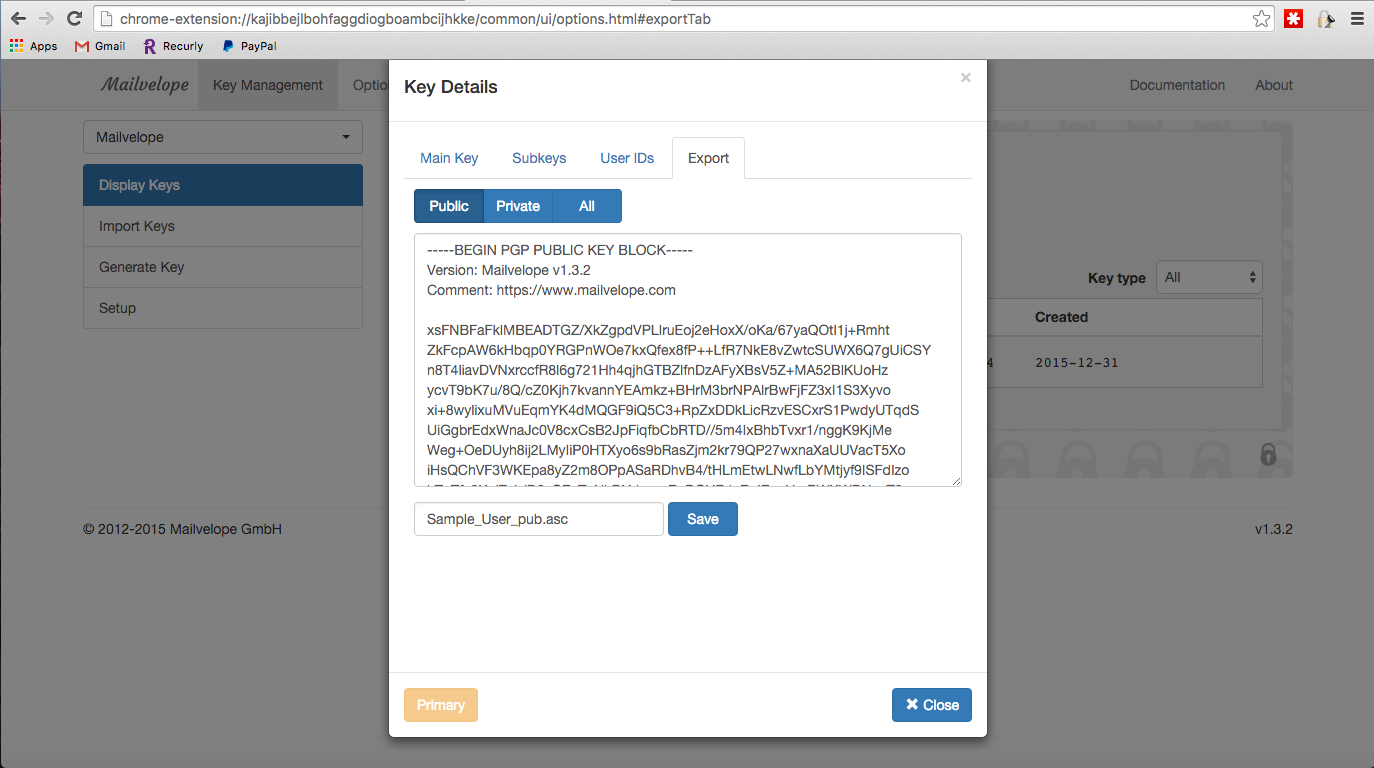 You'll want to share only the PUBLIC key. The private key is what you keep, you never share this. To import, you'll navigate to Import Keys in the menu options and you'll upload the recipients public key. If you want to test it, you can use my public key.
You'll want to share only the PUBLIC key. The private key is what you keep, you never share this. To import, you'll navigate to Import Keys in the menu options and you'll upload the recipients public key. If you want to test it, you can use my public key.
 When you're done, click on Encrypt, and select the individuals you want to encrypt for (hint: you'll need someone else's public key in order for this work.. ) It's important you select your email, and your recipients email; if you don't, you won't be able to read your own email.
When you're done, click on Encrypt, and select the individuals you want to encrypt for (hint: you'll need someone else's public key in order for this work.. ) It's important you select your email, and your recipients email; if you don't, you won't be able to read your own email.
 When you click Ok, you'll see what appears to be a garbled mess:
When you click Ok, you'll see what appears to be a garbled mess:
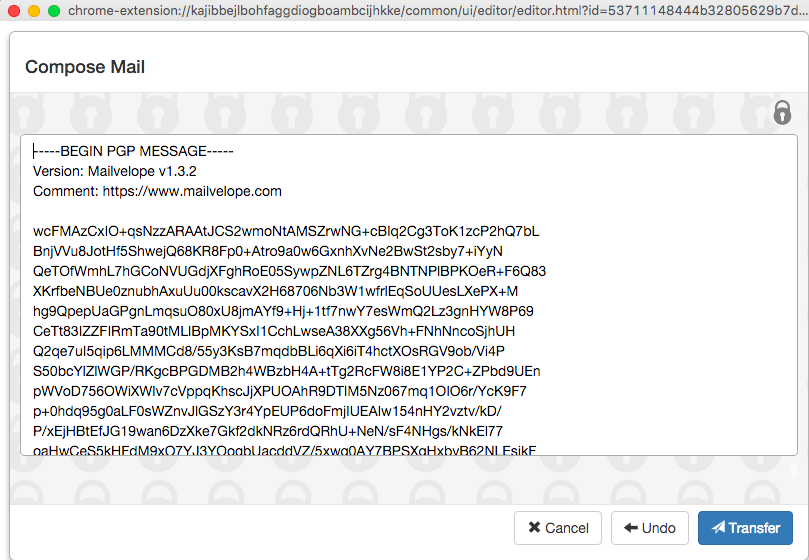 Click on Transfer and the garbled mess will be pushed to the email, ready for you to send to the recipient.
Click on Transfer and the garbled mess will be pushed to the email, ready for you to send to the recipient.
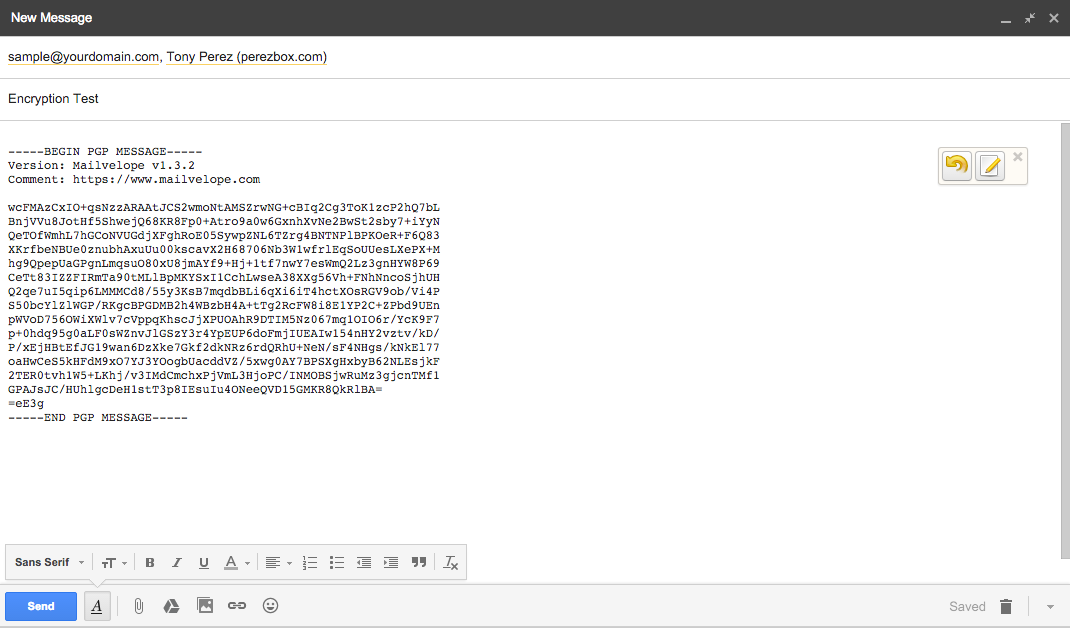 When the recipient receives the message, they'll be able to decrypt the message as long as it was encrypted for the user.
This is what it'll look like when you receive something via the Gmail web client:
When the recipient receives the message, they'll be able to decrypt the message as long as it was encrypted for the user.
This is what it'll look like when you receive something via the Gmail web client: