Posts Tagged ‘WordPress Security’
ANALYZING SUCURI’S 2018 HACKED WEBSITE TREND REPORT
The Sucuri team recently released their second annual security report for 2018 – Hacked Website Report 2018. It looks at a representative sample of infected websites from the Sucuri customer base ONLY. This report helps understand the actions taken by bad actors once they penetrate a website. This report analyzed 25,466 infected websites and 4,426,795 cleaned files; aggregating…
Read MoreAnalyzing Sucuri’s 2017 Hacked Website Trend Report
The Sucuri team just released their first annual security report that looks at telemetry from hacked websites – Hacked Website Report 2017. It uses a representative sample of infected websites from the Sucuri customer base to better understand end-user behavior and bad-actor tactics. It specifically focuses on 34,371 infected websites, aggregating data from two distinct…
Read MoreOpen-Source CMS Security In The Enterprise
Regardless of the size of your organization, the security challenges with open-source Content Management Systems (CMS) security are the same. In the enterprise the issue stems not from the technology or existing processes, but the fact that security is slipping through our fingers. We’ve made it too difficult for our counter parts in marketing and sales, and where there…
Read MoreSecurity In Open-Source CMS Applications
Open-source CMS applications are no stranger to the battle they face with security. The size of the organizations adopting the platform also has little to do with it – from bloggers to mom and pop shops to Fortune 500 companies; the concern is the same. Can open-source CMS applications be deployed securely within their respective stacks? There are…
Read MoreWebsite Security is Not an Absolute
I work in the field of Information Security (InfoSec), specifically website security. With that in mind, it’s but one very small piece of a very large pie. Security is complex, even at the 50,000 foot level; within each specific area of the industry, it can get even more complex. It’s no wonder it can feel…
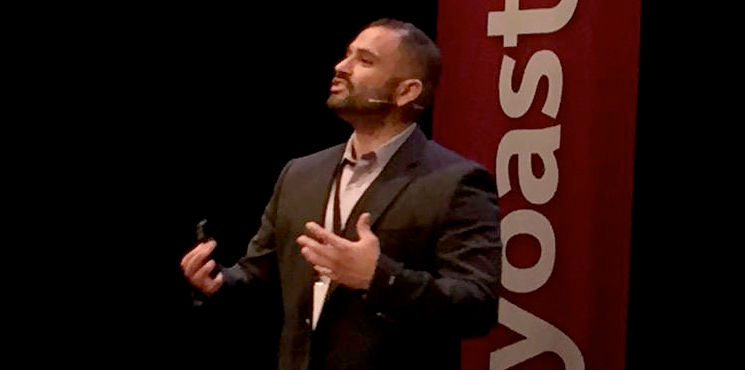
Read MoreYoastCon: The State Of WordPress Security
Almost five years ago, Joost started the company Yoast, offering website reviews and free plugins. Yoast’s core business was, and is, sharing knowledge and making it easier to create usable websites. Five years later Yoast has turned into one of the biggest WordPress plugin providers with 21 employees (and counting)! To celebrate reaching five years,…
Read More